This week should be both interesting and informative! We will talk about online privacy, safety, bullying and consent.
Learning Objectives:
- Be able to explain the concept of digital footprints, and be able to identify what your current personal digital footprint looks like.
- Describe what Orange Shirt Day is and why it is important.
- Identify the key practical issues around online privacy, safety, bullying, and consent as a future K-12 teacher.
Pre-class Activities:
Citizenship Online
 Read the BC provincial government’s Online safety document. Please make sure to click on the “Expand All” button for each section of the document so that you can see all the tips and suggestions. After you finish reading the document please ask yourself:
Read the BC provincial government’s Online safety document. Please make sure to click on the “Expand All” button for each section of the document so that you can see all the tips and suggestions. After you finish reading the document please ask yourself:
- What can you do as a teacher if you become aware of a student being bullied on social media?
- Why should you avoid interacting with your students on social media unless it’s directly related to school work?
- How can we help our learners manage their digital footprints?
Assignment 2 Videos + Q&A Preparation
Please so the following before class time:
- Watch the 4 videos you’ve been assigned to watch :
- Pod 9: How can using GIS tools in the classroom help support students in developing a better understanding of social and physical geography?
- Pod 3: How can fitness technology and activity tracking apps promote healthy habits or unhealthy competition and anxiety among students?
- Pod 4: Old School vs. New School Projects
- Pod 10: Google Gemini as a tool for marking / assessment
- Pod 11: Using Film in Classrooms
- Pod 2: Using Stop-Motion to Support Multimodal Learning
- Pod 15: Can teachers use Slido as an effective way to engage and help students learn?
- As you watch each video write down at least one question for each video and bring the questions with you to class.
- Rich will randomly select two or three people to ask each presenting group questions during class time, so please be prepared for class!
Class Time:
Group EdTech Presentation Summary + Q&A
- Please note that you and your group will have a total of 5-minutes for your presentation summary + Q&A including:
- 3-minutes to summarize your EdTech Video or Audio. You will not be allowed to go over the 2-minute limit for summarizing your work, so please practice your summary to ensure that your summary is not cut short.
- 2-minutes for questions and answers.
- Here is the randomly generated order of the four groups presenting today:
- Pod 9: How can using GIS tools in the classroom help support students in developing a better understanding of social and physical geography?
- Pod 3: How can fitness technology and activity tracking apps promote healthy habits or unhealthy competition and anxiety among students?
- Pod 4: Old School vs. New School Projects
- Pod 10: Google Gemini as a tool for marking / assessment
- Pod 11: Using Film in Classrooms
- Pod 2: Using Stop-Motion to Support Multimodal Learning
- Pod 15: Can teachers use Slido as an effective way to engage and help students learn?
Citizenship Online: Privacy, Safety, Bullying, & Consent
Watch Jesse Miller’s wonderful video on children, social networks, & media literacy (15 min):
Watch the Province of BC’s Digital Footprint video (5 min):
Discussion: What can we do to model good digital citizenship or digital hygiene?
Is My Phone Listening to Me?
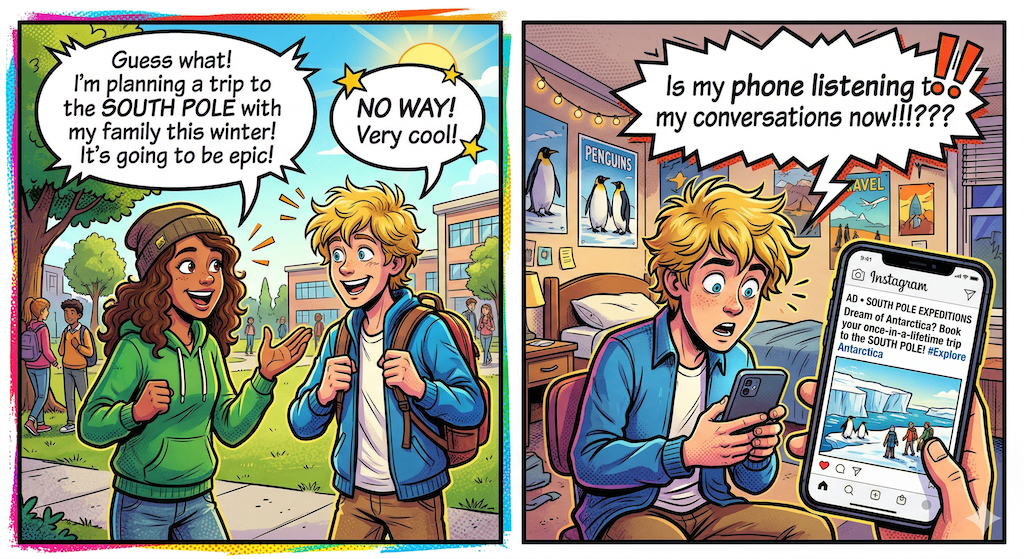 Has this happened to you or someone you know? Your friend mentions that you should take a trip to the south pole, and an hour later, there it is, a “sponsored” post on your feed… And you didn’t Google anything about the South Pole. So what’s happening here? Is your phone listening to you?
Has this happened to you or someone you know? Your friend mentions that you should take a trip to the south pole, and an hour later, there it is, a “sponsored” post on your feed… And you didn’t Google anything about the South Pole. So what’s happening here? Is your phone listening to you?
The Short answer is No. While it feels like your phone must be eavesdropping, the reality is often more complex (and arguably more impressive) than simple audio recording. Here is the “behind the scenes” look at the digital trail that creates that uncanny “listening” effect.
Browser Fingerprinting
Created with Gemini 3.1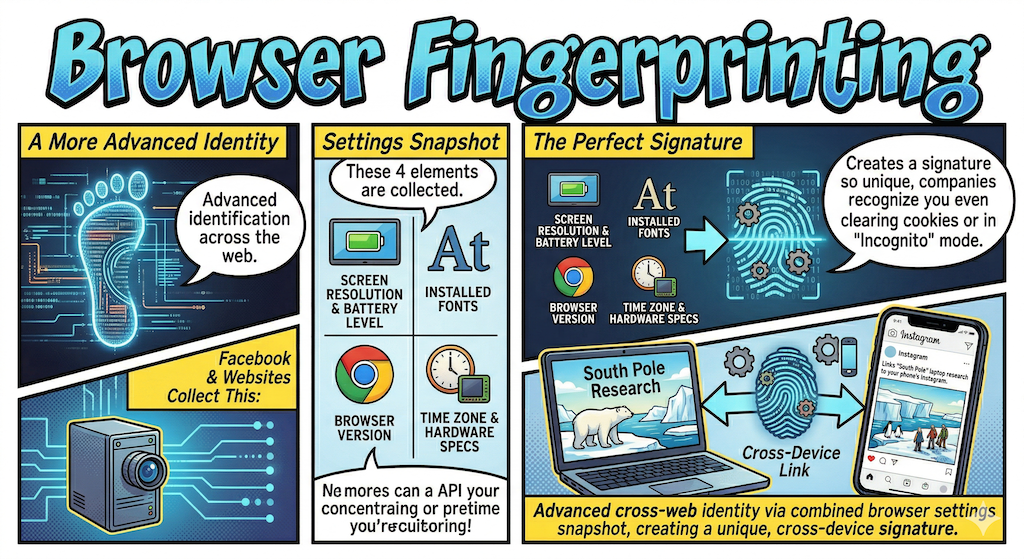 This is a more advanced way to identify you across the web. Some websites (like Facebook) collects a unique “snapshot” of your settings:
This is a more advanced way to identify you across the web. Some websites (like Facebook) collects a unique “snapshot” of your settings:
- Your screen resolution and battery level.
- Installed fonts and browser version.
- Your exact time zone and hardware specifications.
When combined, these traits create a signature so unique that companies can recognize you even if you clear your cookies or use “Incognito” mode. This allows them to link your “South Pole” research on a laptop to the Instagram app on your phone.
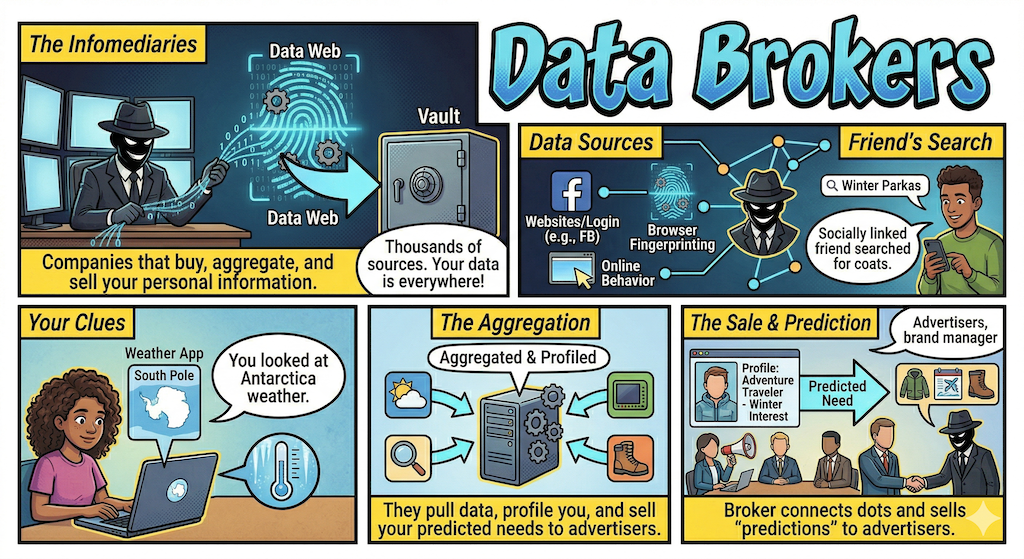
Data Brokers
Data brokers are companies that exist solely to buy, aggregate, and sell your information. They pull data from thousands of sources including websites you go to both when you’re logged in (FB) and sites you browse using Browser Fingerprinting.
When you or your friend talked about the South Pole, you’ve likely already left clues. Maybe you looked at a weather app for Antarctica, or your friend, who is connected to you on social media, searched for “winter parkas.” Data brokers connect these dots and sell the “prediction” to advertisers.
Lookalike Modeling
Created with Gemini 3.1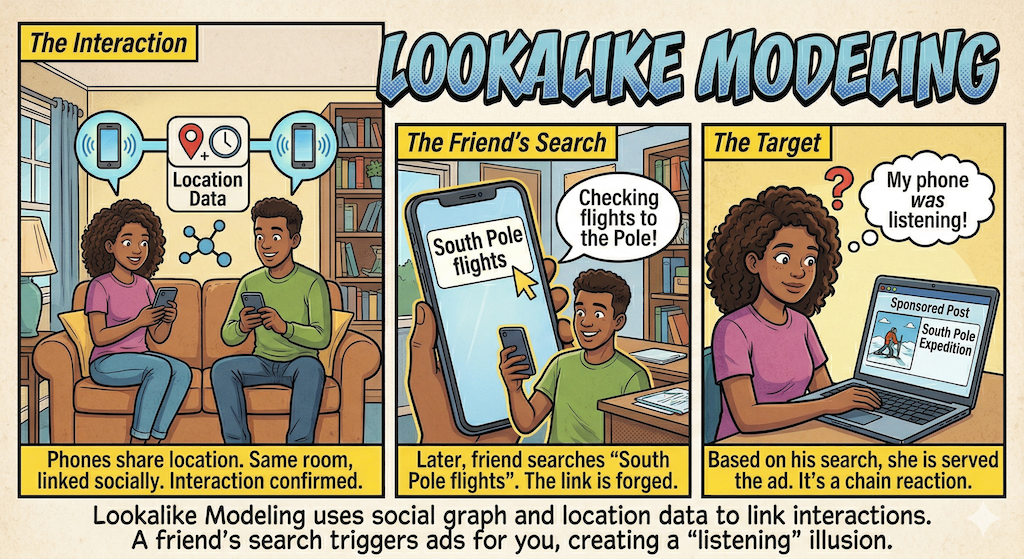 This is the most common reason for the “listening” illusion. Algorithms know your social graph, the people you spend time with.
This is the most common reason for the “listening” illusion. Algorithms know your social graph, the people you spend time with.
- Location Data: If your phone and your friend’s phone are in the same living room for two hours, the algorithm knows you are interacting.
- The Chain Reaction: If your friend goes home and searches for “South Pole flights,” the system assumes you might be interested in the same thing because you were just together. It serves you the ad based on their search.
Myth vs Reality Summary…
| The Myth | The Reality |
| “My phone is recording my voice.” | Constant audio streaming would drain your battery and use massive amounts of data, both of which are easily detectable. |
| “They knew what I was thinking.” | They knew what your friends were searching for and where you were standing. |
| “I never searched for this!” | You didn’t, but you might have bought a related item (like thermal socks) or followed a travel influencer. |
What Can we do?
We can significantly disrupt the “surveillance machine” by cutting off its primary fuel sources: tracking, profiling, and persistent data storage.
Here are three practical steps to protect your digital life in 2026:
1. Kill the “Social Graph” (App Tracking)
The “listening” illusion often happens because apps like Instagram or Facebook link your location to your friends. You can break this chain by disabling cross-app tracking.
-
On iPhone: Go to Settings > Privacy & Security > Tracking and toggle off “Allow Apps to Request to Track.” This prevents apps from accessing your device’s unique Advertising ID (IDFA).
-
On Android: Go to Settings > Privacy > Ads and select “Delete Advertising ID.” This makes it much harder for data brokers to stitch your activity across different apps into one profile.
2. Switch to a “Shielded” Browser
Standard browsers (like Chrome) are designed to facilitate tracking. Switching to a privacy-first browser can stop Browser Fingerprinting by default.
-
Brave or Firefox: These browsers include built-in protections that “randomize” your fingerprint, making your device look like a generic one instead of a unique target.
-
Must-Have Extension: Install uBlock Origin or Privacy Badger. These tools block “trackers” from loading at all, which not only protects your data but also makes your web pages load significantly faster.
3. Evict Yourself from Data Broker Databases
Even if you stop tracking today, data brokers already have years of your history. You can force them to delete it.
-
The Manual Way: You can visit the “Opt-Out” pages of major brokers like Acxiom and Epsilon. I understand that it can be time-consuming but is free.
-
The Automated Way: Use a service like Incogni or DeleteMe, but both of these services charge start at $20 for one month and over $140 per year for their services. These services automatically send legal “Right to Erasure” requests to hundreds of data brokers on your behalf and, critically, keep monitoring to make sure they don’t re-add you later.
Pro Tip: If you want to see exactly how “unique” your browser looks to a tracker right now, visit the EFF’s Cover Your Tracks tool. It will give you a report on how well you’re currently protected against fingerprinting.
Pay The Game!
Is My Phone Listening to me Game
Reflection
After learning about this, do you think you’ll change any of the ways that you use your phone or interact with websites or online?
Hands-on Lab Time:
Learn more about your Digital Footprints & Google yourself:
- Open a new table in your web browser and Google yourself!
- For example, I’d search for: “Rich McCue”, and possibly the city where I live or grew up to the search string if you have popular names: “Rich McCue” Victoria BC
- If you still can’t find any references to yourself, which often happens if you have a common name, add “UVic” to your search string (E.g.: “Tracy Smith” UVic), and see what comes up.
- If possible do your search in “Incognito” or the private mode for your web browser so you can see your search in the way someone else would see it.
- Did you find any web pages or images of yourself?
- Will the web pages or images be helpful during your job search when recruiters search for your name (possibly along with where you live and/or UVic)?
- How can you add positive posts or images that will show up when people search for you on the internet?
- Can web pages or images on the internet be removed?
- What do you think recruiters would think if searched for you but found nothing?
- Do you think that your website for our class could become a portfolio showcasing your best work that school district HR folks could find when they google your name before interviewing you?
Homework:
- Please do your weekly critical reflection on:
- Any one of the digital citizenship topics we’ll cover in class
–OR– - One of the group project topics you review in preparation for this week’s class.
- Any one of the digital citizenship topics we’ll cover in class
- Catch up on any outstanding blog posts!



Leave a Reply